Configure SAML single sign-on with Okta
You can configure your ExtraHop system to enable users to log in to the system through the Okta identity management service.
Before you begin
- You should be familiar with administering Okta. These procedures are based on the Okta Classic UI. If you are configuring Okta through the Developer Console, the procedure might be slightly different.
- You should be familiar with administering ExtraHop systems.
These procedures require you to copy and paste information between the ExtraHop system and the Okta Classic UI, so it is helpful to have each system open side-by-side.
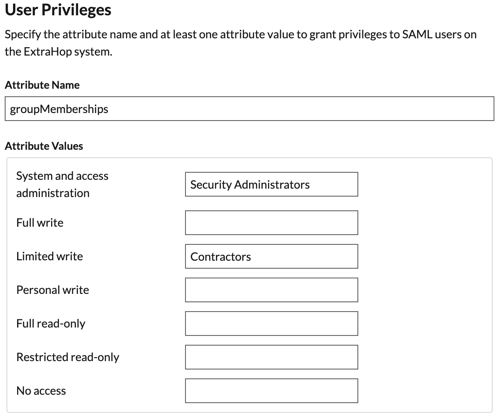
Enable SAML on the ExtraHop system
- Log in to the Administration settings on the ExtraHop system through https://<extrahop-hostname-or-IP-address>/admin.
- In the Access Settings section, click Remote Authentication.
- From the Remote authentication method drop-down list, select SAML.
- Click Continue.
- Click View SP Metadata. You will need to copy the ACS URL and Entity ID to paste into the Okta configuration in the next procedure.
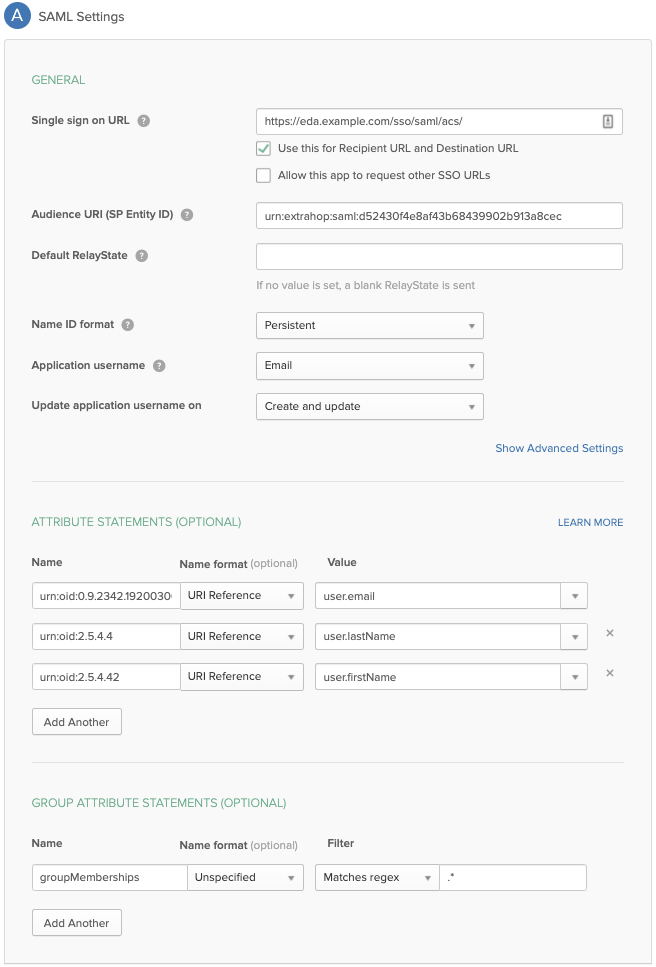
Configure SAML settings in Okta
This procedure requires you to copy and paste information between the ExtraHop Administration settings and the Okta Classic UI, so it is helpful to have each UI open side-by-side.
Assign the ExtraHop system to Okta groups
We assume that you already have users and groups configured in Okta. If you do not,
refer to the Okta documentation to add new users and groups.
- From the Directory menu, select Groups.
- Click the group name.
- Click Manage Apps.
- Locate the name of the application you configured for the ExtraHop system and click Assign.
- Click Done.
Thank you for your feedback. Can we contact you to ask follow up questions?