Threat intelligence
Threat intelligence provides known data about suspicious IP addresses, domains, hostnames, and URIs that can help identify risks to your organization.
| Video: | See the related training: Threat Intelligence |
Threat intelligence data sets, called threat collections, contain lists of suspicious endpoints known as indicators of compromise (IOCs).
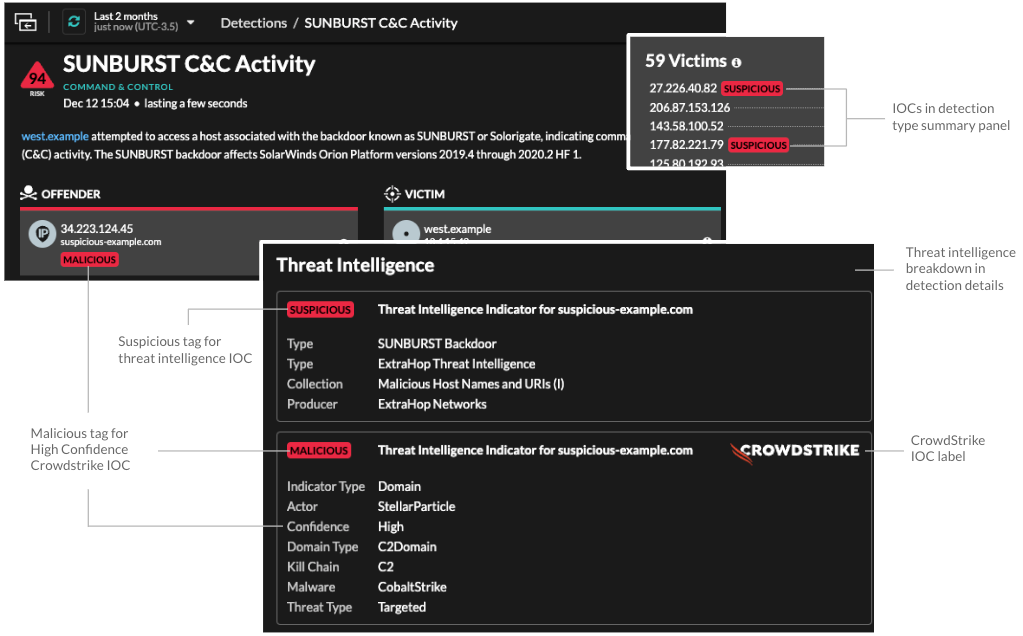
Participants that match a threat collection are tagged as Suspicious in
detections, detection summaries, system charts, and records. (For
Crowdstrike IOCs where the confidence level is High, the participant is
tagged as Malicious.) Records that contain the suspicious entry are marked
with a camera icon  . In many cases, an indicator match also generates a detection for the
suspicious connection.
. In many cases, an indicator match also generates a detection for the
suspicious connection.
Threat collections
The ExtraHop system supports threat collections from several sources.
- Built-in threat collections
- Curated threat collections from ExtraHop and CrowdStrike Falcon are available by default in your ExtraHop system. Built-in collections are updated every 6 hours. You can enable or disable built-in threat collections from the Threat Intelligence page.
- STIX file uploads
- Free and commercial collections offered by the security community that are formatted in Structured Threat Information eXpression (STIX) as compressed TAR files, such as .TGZ or TAR.GZ, can be uploaded manually or through the REST API to ExtraHop systems. STIX version 1.0 - 1.2 are currently supported. You must upload each threat collection individually to your console and all connected sensors.
- TAXII feed
- Threat collections can be delivered to your environment from a reliable source over the Trusted Automated Exchange of Intelligence Information (TAXII) protocol. A TAXII feed can provide a consistent stream of updated threat indicators. You can add a TAXII feed from the Threat Intelligence page.
Investigating threats
After the Reveal(x) system observes an indicator of compromise, the suspicious IP address, domain, hostname, or URI is marked as Suspicious or Malicious in detection summaries and on individual detection cards. In tables and charts, indicators of compromise are marked with a camera icon so you can investigate directly from the tables and charts you are viewing.
- If the threat collection is added or updated after the system has observed the suspicious activity, threat intelligence is not applied to that IP address, hostname, or URI until the suspicious activity occurs again.
- (Reveal(x) 360 only) If a built-in ExtraHop or CrowdStrike threat collection is updated, the ExtraHop system performs Automated Retrospective Detection (ARD), which searches for new domains, hostnames, URLs, and IP addresses that are indicators of compromise in records for the past 7 days. If a match is found, the system generates a retrospective detection.
- If you disable or delete a threat collection, all indicators are removed from the related metrics and records in the system. Detections that are recommended for triage based on threat intelligence will remain in the system after the associated collection is disabled.
Here are some places in the Reveal(x) system that show the indicators of compromise found in your threat collections:
Security Hardening Dashboard
The Threat Intelligence region contains
metrics for suspicious activity that matches the data in your threat collections. By clicking
any metric, such as HTTP Requests with Suspicious Hosts, you can drill down on the metric for
details or query records for related transactions.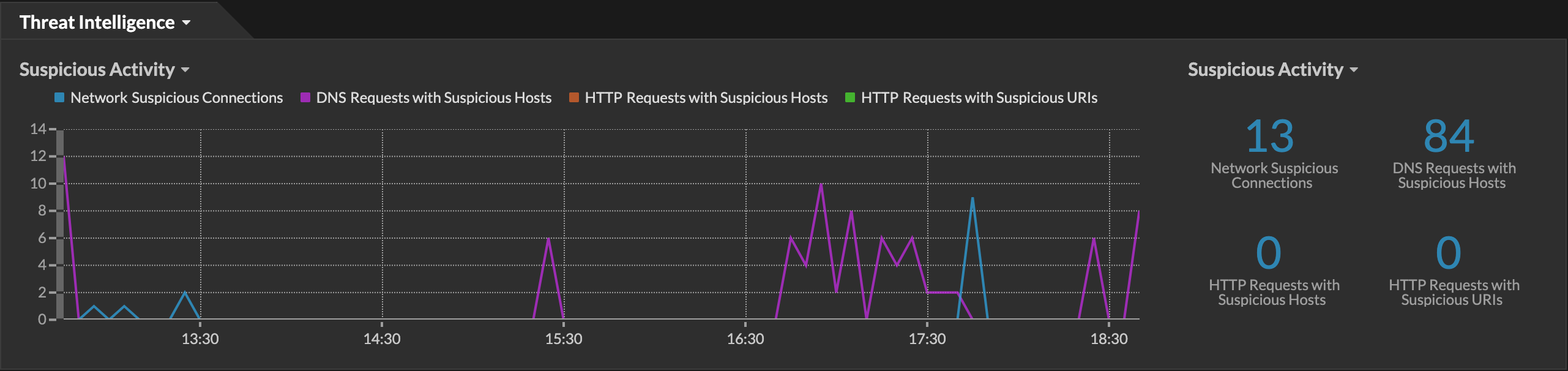
Perimeter Overview
In the halo visualization, any endpoints that match threat collection entries are highlighted
in red. 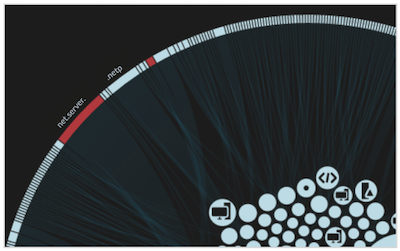
Detections
A detection appears when an indicator of compromise from a threat collection is identified in
network traffic. 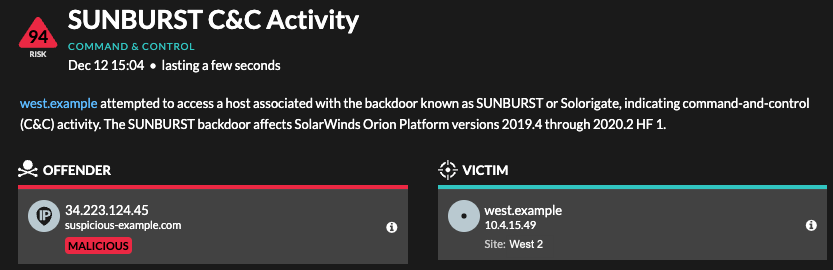
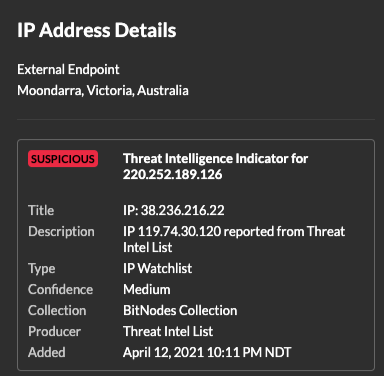
IP Address Details
IP address detail pages display complete threat intelligence for IP address indicators of
compromise.
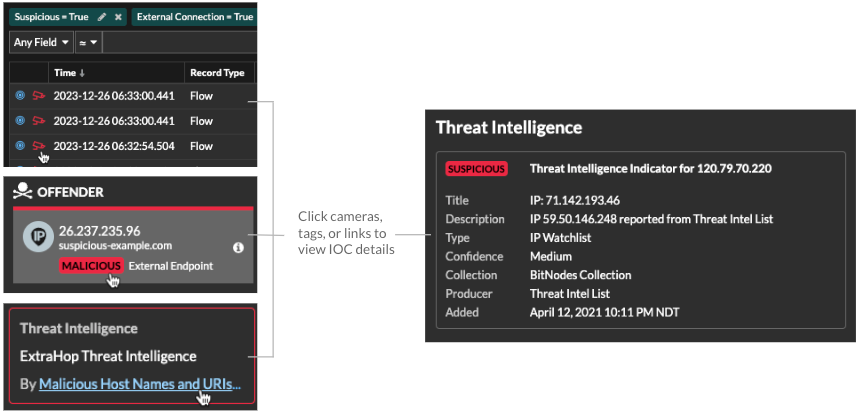
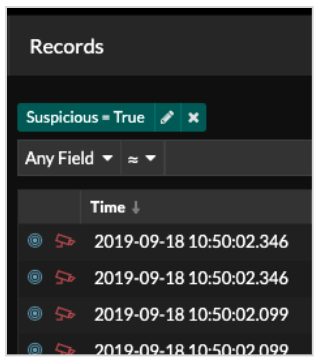
Records
- Under the Suspicious facet, click True to filter for all records with transactions that match suspicious IP addresses, hostnames, and URIs.
- Create a filter by selecting Suspicious, Suspicious IP, Suspicious Domain, or Suspicious URI from the trifield drop-down, an operator, and a value.
- Click the red camera icon
 to
view threat intelligence.
to
view threat intelligence.
Retrospective detections
(Reveal(x) 360 only) When an ExtraHop or CrowdStrike threat collection is updated, the ExtraHop system performs Automated Retrospective Detection (ARD), which searches for new domains, hostnames, URLs, and IP addresses that are indicators of compromise in records for the past 7 days. If a past connection to a suspicious domain is identified, the system generates a retrospective detection.
The timestamp on a retrospective detection indicates the time that the activity originally occurred and might not appear in the current detection list. You can find retrospective detections by clicking on the Retrospective Threat Intelligence threat briefing. You can also create a detection notification rule to email you when these types of detections occur.
Thank you for your feedback. Can we contact you to ask follow up questions?