Download session keys with packet captures
You can download PCAP Next Generation (pcapng) file that includes all captured SSL session keys for SSL packet captures. Then, you can download and open the associated packet capture file with a packet analysis tool like Wireshark that can display the decrypted payload.
Before you begin
- You must have a configured packetstore before you can download packets and session keys from a sensor or a console. See our deployment guides to get started.
- The console must be licensed for SSL Shared Secrets.
- The SSL Session Key Storage setting must be enabled on the sensor.
- Reveal(x) Enterprise users must have either system access and administration privileges or limited privileges with packets and session keys access. Reveal(x) 360 users must have packets and session keys access.
View the decrypted payload in Wireshark
- Start the Wireshark application.
- Open the downloaded packet capture (pcapng) file in Wireshark.
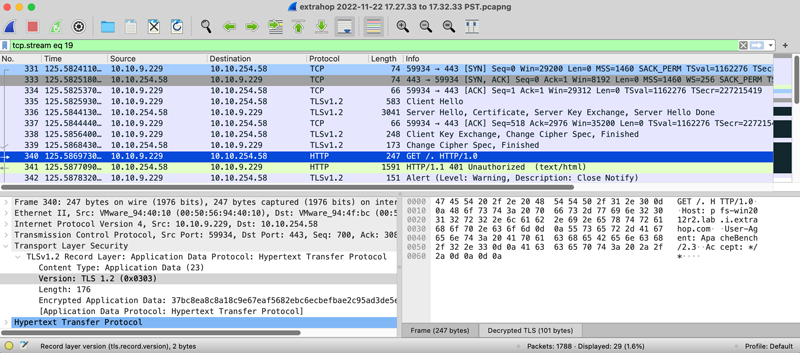
When an SSL-encrypted frame is selected, the Decrypted SSL tab appears at the bottom of the Wireshark window. Click the tab to see the decrypted information in the packet capture as plain text.
Thank you for your feedback. Can we contact you to ask follow up questions?