Packets
A network packet is a small amount of data sent over Transmission Control Protocol/Internet Protocol (TCP/IP) networks. The ExtraHop system enables you to continuously collect, search, and download these packets with a Trace appliance, which can be useful to detect network intrusions and other suspicious activity.
You can search for and download packets from the Packets page in the ExtraHop system and through the Packet Search resource in the ExtraHop REST API. Downloaded packets can then be analyzed through a third-party tool, such as Wireshark.
| Note: | If you do not have a Trace appliance, you can still collect packets through triggers. See Initiate precision packet captures to analyze zero window conditions for an example. |
Launch a quick packet query by clicking Packets from the top menu. The ExtraHop system queries for all packets and displays the Packet Query page. If you change the time interval, the query starts again. Either end of the gray bar displays a timestamp, which is determined by the current time interval. The time on the right displays the starting point of the query and the time on the left displays the endpoint of the query. The blue bar indicates the time range during which the system found packets. You can drag to zoom on a period of time in the blue bar to run a query again for that selected time interval.
The following figure provides an overview of the Packet Query page and features:
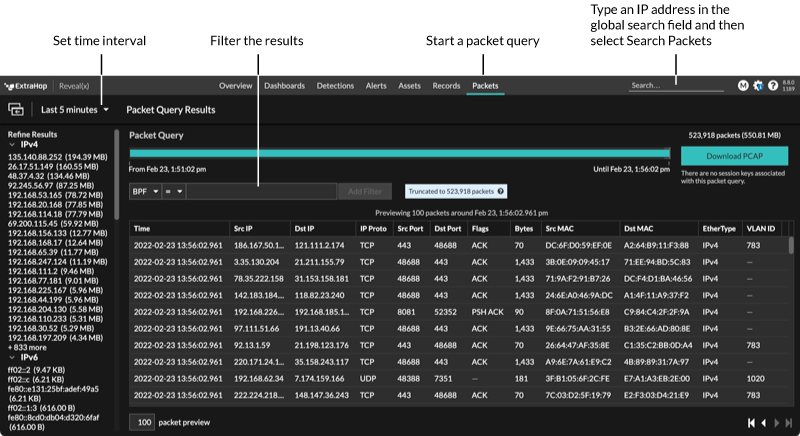
| Tip: | Filter packets with Berkeley Packet Filter syntax. |
There are multiple locations in the ExtraHop system from which you can initiate a packet query:
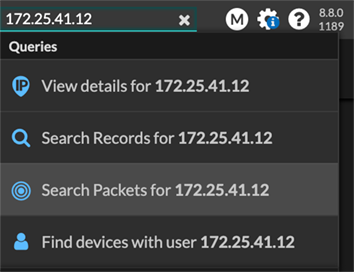
- Type an IP address in the global search field and then select the Search Packets
icon
 .
.
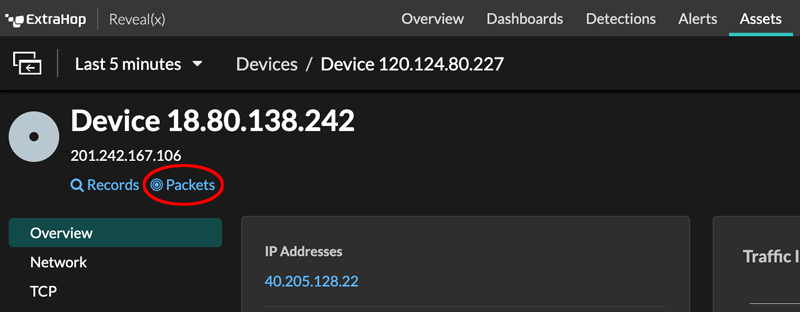
- Click Packets on a device page.
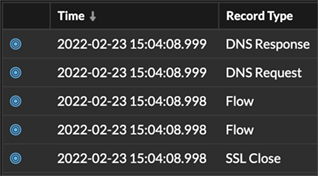
- Click the Packets icon
 next to any record on a record query results page.
next to any record on a record query results page.
- Click on an IP address or hostname in any chart with metrics for network bytes
or packets by IP address to see a context menu. Then, click the Packets icon
 to query for the device and time interval.
to query for the device and time interval.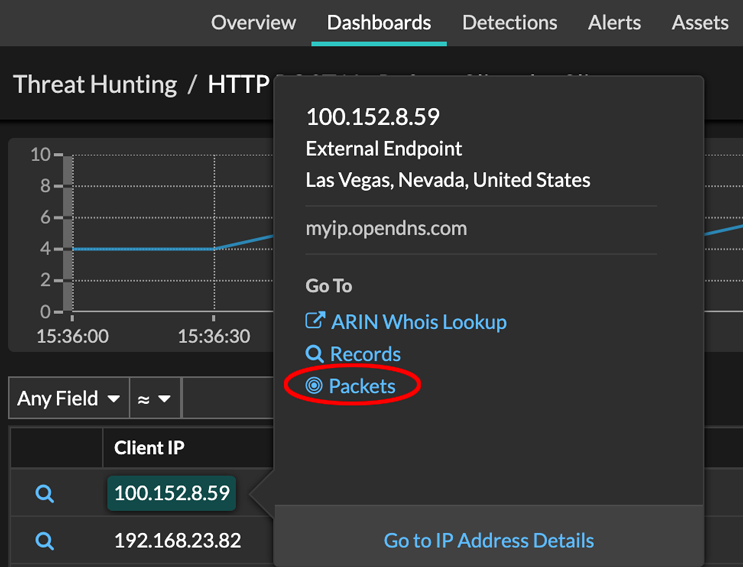
Thank you for your feedback. Can we contact you to ask follow up questions?