Decrypt domain traffic with a Windows domain controller
The ExtraHop system can be configured to retrieve and store domain keys from a domain controller. When the system observes encrypted traffic that matches the stored keys, all of the Kerberos-encrypted traffic in the domain is decrypted for supported protocols. The system only synchronizes Kerberos and NTLM decryption keys and does not modify any other properties in the domain.
A domain controller like Active Directory is a frequent target for attackers because a successful attack campaign yields high-value assets. Critical attacks can be obscured by Kerberos or NTLM decryption, such as Golden Ticket, PrintNightmare, and Bloodhound. Decrypting this type of traffic can provide deeper insight for security detections.
You can enable decryption on an individual sensor or through an integration on Reveal(x) 360.
The following requirements must be met for decryption:
- You must have an Active Directory domain controller (DC) that is not configured as a Read-only Domain Controller (RODC).
- Only Windows Server 2016 and Windows Server 2019 are supported.
- Only one domain controller can be configured on a sensor, which means you can decrypt the traffic from one domain per sensor.
- The ExtraHop system synchronizes keys for up to 50,000 accounts in a configured domain. If your DC has more than 50,000 accounts, some traffic will not be decrypted.
- The ExtraHop system must observe the network traffic between the DC and connected clients and servers.
- The ExtraHop system must be able to access the domain controller over the following ports: TCP 88 (Kerberos), TCP 445 (SMB), TCP 135 (RPC), and TCP ports 49152-65535 (RPC dynamic range).
| Warning: | If you enable these settings, the ExtraHop system is granted access to
all of the account keys in the Windows domain. The ExtraHop system should be deployed at
the same security level as the domain controller. Here are some best practices to
consider:
|
Connect a domain controller to a sensor
Before you begin
You must have a user account with Unlimited privileges on the sensor.Connect a domain controller to a Reveal(x) 360 sensor
Before you begin
Your user account must have privileges on Reveal(x) 360 for System and Access Administration or Cloud Setup.Validate the configuration settings
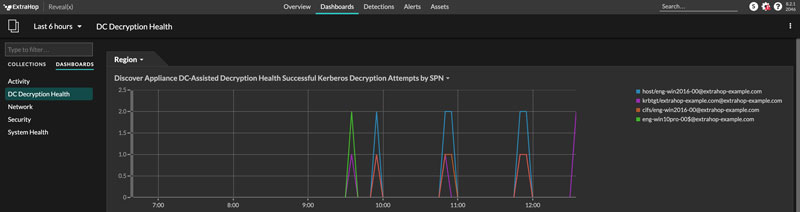
To validate that the ExtraHop system is able to decrypt traffic with the domain controller, create a dashboard that identifies successful decryption attempts.
- Create a new dashboard.
- Click the chart widget to add the metric source.
- Click Add Source.
- In the Sources field, type the name of the sensor communicating with a domain controller and then select the sensor from the list.
- In the Metrics field, type DC in the search field and then select DC-Assisted Decryption Health - Successful Kerberos Decryption Attempts by SPN.
- Click Save.
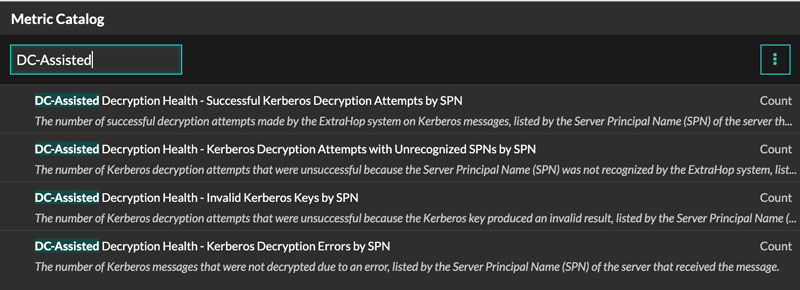
Additional system health metrics
To view
a list of available metrics, click the System Settings icon ![]() and then click Metric Catalog. Type
DC-Assisted in the filter field to display all
available DC-assisted decryption metrics.
and then click Metric Catalog. Type
DC-Assisted in the filter field to display all
available DC-assisted decryption metrics.
Thank you for your feedback. Can we contact you to ask follow up questions?