Configure SAML single sign-on with Google
You can configure your ExtraHop system to enable users to log in to the system through the Google identity management service.
Before you begin
- You should be familiar with administering Google Admin.
- You should be familiar with administering ExtraHop systems.
These procedures require you to copy and paste information between the ExtraHop system and Google Admin console, so it is helpful to have each system open side-by-side.
Add user custom attributes
- Log in to the Google Admin console.
- Click Users.
-
Click the Manage custom attributes icon
 .
.
- Click Add Custom Attribute.
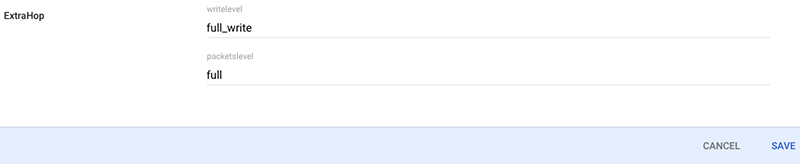
- In the Category field, type ExtraHop.
- (Optional): In the Description field, type a description.
-
In the Custom fields section, enter the following
information:
- In the Name field, type writelevel.
- From the Info Type drop-down menu, select Text.
- From the Visibility drop-down menu, select Visible to domain.
- From the No. of values drop-down menu, select Single Value.
-
Enable NDR module access:
- In the Name field, type ndrlevel.
- From the Info Type drop-down menu, select Text.
- From the Visibility drop-down menu, select Visible to domain.
- From the No. of values drop-down menu, select Single Value.
-
Enable NPM module access:
- In the Name field, type npmlevel.
- From the Info Type drop-down menu, select Text.
- From the Visibility drop-down menu, select Visible to domain.
- From the No. of values drop-down menu, select Single Value.
- (Optional):
If you have connected packetstores, enable packet access by configuring a
custom field:
- In the Name field, type packetslevel.
- From the Info Type drop-down menu, select Text.
- From the Visibility drop-down menu, select Visible to domain.
- From the No. of values drop-down menu, select Single Value.
- Click Add.
 .
.
Thank you for your feedback. Can we contact you to ask follow up questions?