Manage threat collections
ExtraHop Reveal(x) can apply threat
intelligence to your network activity based on threat collections provided by
Extrahop, partner integrations, or other free and commercial sources.
To add threat intelligence from CrowdStrike, see Integrate Reveal(x) 360 with CrowdStrike.
Before you begin
- Learn about threat intelligence.
- You must have System and Access Administration privileges on each console and sensor to manage threat collections.
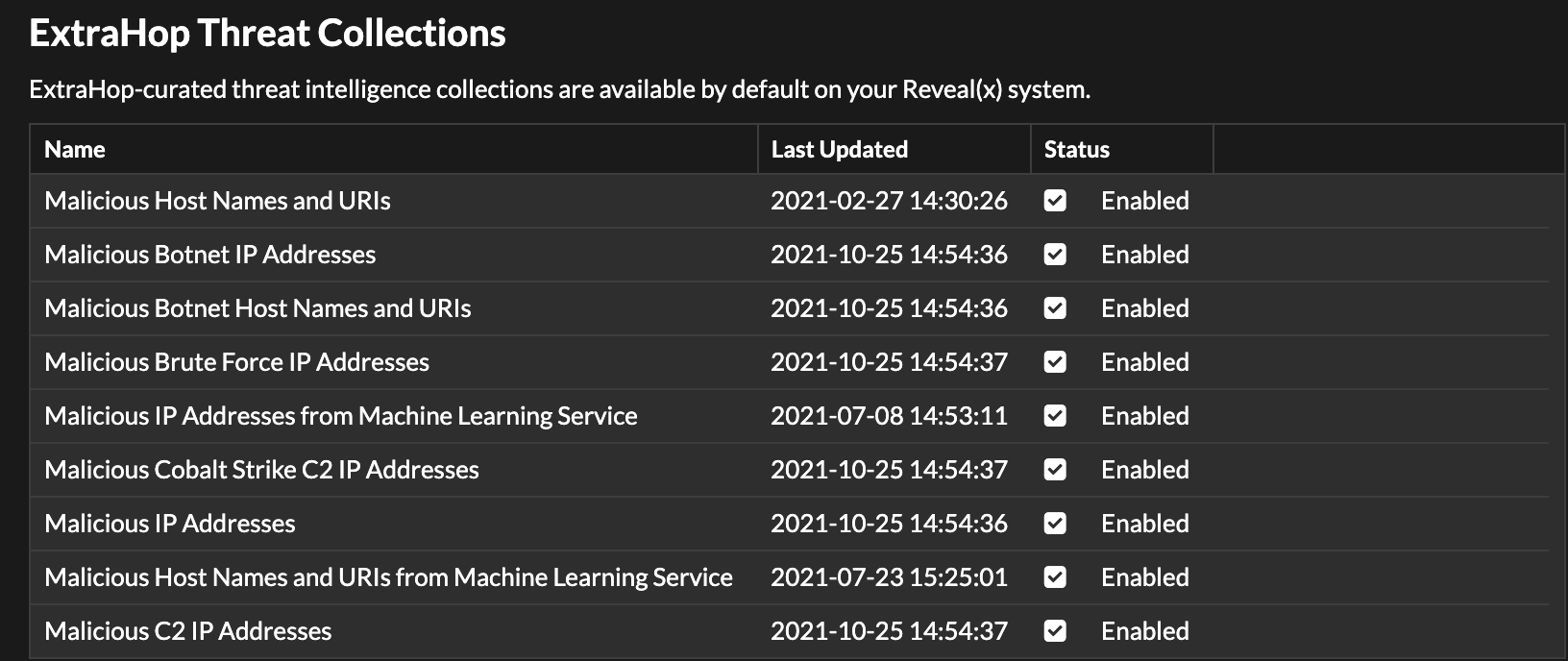
Enable or Disable ExtraHop-curated threat collections
ExtraHop threat collections are enabled by default and identify indicators of compromise throughout the system.
ExtraHop threat collections automatically update
systems that are connected to ExtraHop Cloud Services. You can confirm connectivity
on the ExtraHop Cloud Services
page in the Administration settings.
Upload a threat collection
Upload threat collections from free and commercial sources to identify indicators of compromise throughout the ExtraHop system. Because threat intelligence data is updated frequently (sometimes daily), you might need to update a threat collection with the latest data. When you update a threat collection with new data, the collection is deleted and replaced, and not appended to an existing collection.
You must upload threat collections individually to
your console, and to all connected sensors.
Here are some considerations about
uploading threat collections.
- Custom threat collections must be formatted in Structured Threat Information eXpression (STIX) as TAR.GZ files. Reveal(x) currently supports STIX version 1.0 - 1.2.
- You can directly upload threat collections to Reveal(x) 360 for self-managed sensors. Contact ExtraHop Support to upload a threat collection to ExtraHop-managed sensors.
- The maximum number of observables that a threat collection can contain depends on your platform and license. Contact your ExtraHop representative for more information.
- You can upload STIX files through the REST API.
- Log in to the ExtraHop system through https://<extrahop-hostname-or-IP-address>.
-
Click the System Settings icon
 and then click Threat
Intelligence.
and then click Threat
Intelligence.
- Click Manage custom collections.
- Click Upload New Collection.
- In the Collection ID field, type a unique collection ID. The ID can only contain alphanumeric characters and spaces are not allowed.
- Click Choose file and select a .tgz file that contains a STIX file.
- Type a display name in the Display Name field.
- Click Upload Collection.
- Repeat these steps for each connected sensor and on all consoles.
Thank you for your feedback. Can we contact you to ask follow up questions?